- 12 minutes 4 secondsThe Instant Payments Shift Is Testing the Limits of Legacy Banking

For decades, banks could afford to move slowly. Now, speed is table stakes. In a world of instant payments and real-time expectations, institutions built on legacy systems are being forced to confront a hard reality: modernizing is no longer optional.
In a PaymentsJournal Podcast, George Malesky, Director of Partnership Development at Qualpay, and Brian Riley, Co-Head of Payments at Javelin Strategy & Research, discussed what legacy banks are up against as instant payments become the norm. For institutions whose technology stacks need an overhaul, the options may not be ideal, but at least they exist.
Focusing on the Big Picture
When a bank tries to do everything at once, it typically ends up doing very little well. The first step toward modernization is defining a clear focus. Banks need to identify operational efficiencies and determine which upgrades will create the most leverage and opportunity.

This isn’t just about driving growth. Strengthening compliance and risk management systems is equally critical. While improvements in sales and customer experience can attract new business, foundational operational enhancements are what makes that growth sustainable.
“You’re not going to totally disrupt your core, or completely overhaul your system,” said Malesky. “But you can make things like onboarding and payments and servicing better by making sure they have updated technology.”
Getting Ready for Instant Payments
On top of existing challenges, banks must now prepare for a world of faster payments. Neither regulators nor customers are willing to accept institutions that can’t keep pace.
Speed alone isn’t the solution. Banks need the right technology and the underlying architecture to support it. Just as important is adopting a forward-looking mindset—one that anticipates future demands, especially when competing with more agile fintechs.
“You have to make sure everything works together, that the APIs and the middleware all talk together well,” said Malesky. “Sometimes it’s more about thinking of a way to work around your core rather than replacing it or going through it.”
Too often, banks overestimate the strategic value of owning their payment infrastructure while underestimating its cost. The burden extends beyond upfront investment to include complexity, ongoing maintenance, regulatory requirements, scheme updates, fraud management, and continuous innovation.
What’s critical here is treating payments as a strategic capability—not necessarily a fully owned asset. In-house solutions can offer control and customization, but they come with significant trade-offs in cost and operational burden.
Looking for a Partner
Some banks, with sufficient capital and internal resources, may choose to modernize their payment systems independently. However, many are finding success by partnering with providers that bring both experience and modern platforms.
These partnerships can accelerate transformation timelines.
“Everyone knows the old adage that every journey begins with a single step,” said Malesky. “But when it comes to siloed systems and fragmented tools, maybe it’s a handful of steps to get there at the forefront. There’s not necessarily a single bullet or a single provider that can do absolutely anything and everything that a bank will need, but you want to reduce vendor clutter and some of the complexities by having single source solutions.”
Breaking Down Silos
Partnering can speed up modernization, but it doesn’t eliminate one of the industry’s most persistent challenges—siloed systems.
Embedded solutions can reduce distractions and minimize errors, but they don’t always integrate smoothly with adjacent systems. Both legacy and modern platforms must communicate effectively to deliver real value.
Siloed systems create friction across the organization. Customers may struggle to navigate disconnected services, while banks face inefficiencies such as duplicated data and redundant processes. The impact is far-reaching.
“When a bank is not operating as one holistic system, it loses opportunities to cross sell,” said Riley. “You’re losing a line of sight on the true risk of a customer, whether there’s loans or deposits involved. They don’t necessarily have to work together, but when they do, it’s a much better experience for everyone, especially the operational people and of course the customer.”
One clear example is onboarding. Fintechs can onboard customers in minutes, while traditional banks may take up to seven days—and at two to three times the cost for merchant accounts.
“It’s really a challenge if you’re going to be that slow,” said Malesky. “When we used to text in the early stages of flip phones, we had to open up our phone and press the number 2 three times to get the letter C. It was a slow, monotonous process. But in those days, we didn’t know any different. We didn’t know what was coming with iPhones.”
Fintechs are effectively delivering the “smartphone experience” of financial services. Once customers become accustomed to that level of speed and convenience, it’s difficult to revert. If banks can’t meet those expectations, customers will look elsewhere.
Where Are Banks Heading?
Modernizing a legacy banking system involves many moving parts. It’s not enough to address current needs, banks must also align their upgrades with long-term strategic goals.
“Unless you’re ready for the future, you will not get through it,” said Riley. “It’s not just ‘Let’s get to it on a 10-year plan.’ It’s where you’re looking to go, and how quickly will you get there.”
Malesky added: “Think ahead to how you can make the customer experience that much better because that translates into more customers, and more usage for existing customers. And that’s the goal for most banks.”
[contact-form-7]The post The Instant Payments Shift Is Testing the Limits of Legacy Banking appeared first on PaymentsJournal.
26 May 2026, 1:00 pm - 13 minutes 57 secondsEmbedded Payments Are Becoming Core to Vertical SaaS

Not long ago, a concrete company and a takeout restaurant could end up running their business on the exact same software. Systems built for everyone, in practice, worked perfectly for no-one—and bending them to fit the realities of a small business was often frustrating or simply impossible.
Vertical software-as-a-service (SaaS) solutions emerged to solve this problem, quickly evolving from the exception to the norm. The reasons for this growth are largely self-evident: vertical SaaS enables rapid implementation with minimal customization. In many cases, merchants feel these platforms are built for their business rather than retrofitted to it. However, the operational benefits of SaaS are diminished if payments aren’t integrated into the solution.
In a recent PaymentsJournal podcast, Brad Pinneke, Head of Enterprise Development at Worldpay, now Global Payments, and Don Apgar, Director of Merchant Payments at Javelin Strategy and Research, discussed how embedded payments have become a critical driver of vertical SaaS—a synergy that will only strengthen as new trends and technologies reshape the landscape.
The Case for Embedded Payments
One of the most notable aspects of the rise of vertical SaaS is that it has largely been market-driven. Adoption has accelerated as industries not typically known as early adopters—such as healthcare, construction, and financial services—have come on board, despite heavy compliance and consumer protection requirements.

With the advantages of vertical SaaS now well established, these platforms will continue gaining traction and carving out new niches.
“POS systems were so generic that everybody had to customize it, and most merchants were finding that that customization wasn’t possible because the platform didn’t support the features that they needed for their business,” Apgar said. “Now that these features are being identified, it’s created these micro-markets for POS platforms to be focused on the needs of specific business types, and payments are part and parcel with that.”
Payments are a logical addition, given that vertical SaaS solutions increasingly encompass nearly every aspect of a small business. A pizzeria’s platform, for example, may manage everything from payroll to inventory.
Yet few functions are as mission-critical as payments. This is why embedded payments and vertical software are increasingly in lockstep. By embedding payments directly into workflows, businesses can complete transactions at the exact moment a customer is ready to pay—whether when a service is completed or a product is purchased.
“I’ll give you a great example from the last couple of years: field services,” Pinneke said. “In the past, the tech used to complete the job and then the office staff would send an invoice and the payment would arrive weeks later. Then, they have to reconcile that payment, take it to the bank, and cash flow was unpredictable.”
“Fast forward to today, where embedded technology comes into play,” he said. “The job is marked complete, the payment is scheduled instantly, the receipt is automatically sent out, and the funds are settled predictably. You’re limiting the back-office intervention, which has huge impact to smaller businesses.”
Automatic, Not Forensic
One of the benefits of vertical SaaS solutions is the ability to deliver holistic business insights through a unified dashboard. Embedded payments extend this value far beyond checkout.
“The embedded impact is that things like payouts and fees and balances are visible alongside operational metrics,” Pinneke said. “In the past, you had the system of record showing one thing and then you had a payments portal showing something else and the reconciliation between those was tough.”
“That’s a big part of it today—it’s automatic, not forensic,” he said. “Forensic was such a big part of small business challenges; they just didn’t have time. Now, the reporting reflects reality, not just an estimate, and that’s critical for businesses today.”
When implemented correctly, this seamless integration can improve cash flow while streamlining the customer experience.
However, these gains depend on thoughtful placement within the platform. Payments should not exist as a separate or disjointed process; instead, sales, onboarding, and customer experience should reinforce a single, cohesive journey.
Equally important is timing. Successful platforms introduce payments early in the customer lifecycle. Too often, organizations treat payments as an afterthought—only addressing them once users are trained and ready to deploy the solution.
In short, platforms that succeed with embedded payments don’t position them as a value-add—they treat them as critical infrastructure that completes the workflow.
“When POS evolved into vertical SaaS, it wasn’t uncommon for the merchant to say, ‘I’m going to shop for my software and now I’m going to shop for my payment solution,’” Apgar said. “Successful SaaS providers have figured out that it’s not a check-the-box optional feature. A lot of what’s driving the move toward embedded finance is that the vertical SaaS software is enabling a single source of truth database—starting with payments and eventually evolving into supplier payments and other functions that work off that same data set.”
“It’s critical to the functionality of the system to drive off that single data set to have payments embedded in the SaaS solution,” he said. “The SaaS company has to embrace that and make that part of the go-to market strategy. It’s not a bolt-on or an add-on, it’s core to the function of the platform.”
The Time Resource
Merchants and platforms that embrace embedded payments as a core component of vertical SaaS will be better equipped not only for today’s challenges but also for a future shaped by artificial intelligence.
“For the SMB that is the typical vertical SaaS user, AI is going to be a game changer,” Apgar said. “The most critical resource in the life of the business owner is time. With the centralized dataset within the vertical SaaS platform, the common option has been to create dashboards. So, we create marketing dashboards and payment dashboards and cash flow dashboards and say, ‘Here’s all the information that the business owner needs.’”
“The bottom line is the business owner doesn’t have time to sit there and sift through all this,” he said. “That’s what AI does best, it manages large volumes of data to impute trends and make recommendations.”
AI-driven decisioning is especially valuable at key points in financial workflows where human intervention can be slow and costly—such as determining whether funds should be released.
Rather than relying on manual review, AI can sift and analyze vast datasets to flag suspicious or high-risk transactions, then approve, deny, or delay them accordingly. This helps financial institutions meet growing demands for real-time transactions while maintaining strong fraud protections.
AI also plays a crucial role in payments orchestration, selecting the optimal payment rail based on factors like cost or efficiency. As new payment methods emerge, AI will become increasingly central in determining the best route for each transaction.
From Reactive to Proactive
Ultimately, AI is shifting organizations from reactive reporting to proactive insights. Historically, businesses often accessed key data weeks or months after the fact. Today, AI can process information in real-time, transforming areas such as predictive risk assessment and exception handling.
These efficiency gains also create opportunities for cost reduction, including areas that directly impact merchants’ bottom lines.
“AI feels like back when reliable internet became available, it’s such a driving force today,” Pinneke said. “The number one thing I get asked is ‘How do we handle chargebacks?’ If you look at AI, there is probably the greatest opportunity to let AI engines figure out the chargebacks in real time and deal with them.”
“If you think about the entire process, it’s essentially broken,” he said. “People dispute something, it comes back, and the merchant and retailer has to go and collect data and show proof and all of that,” he said. “Imagine if AI tools did more of the upfront work. We would probably see a lot less chargebacks, and that turns into real dollars. That’s probably the number one place where AI is making a difference for everybody up and down the food chain.”
[contact-form-7]The post Embedded Payments Are Becoming Core to Vertical SaaS appeared first on PaymentsJournal.
20 May 2026, 1:00 pm - 23 minutes 54 secondsInside Banking’s $10 Billion Inflection Point

Crossing $10 billion in assets isn’t just a milestone for financial institutions—it’s a turning point. What looks like a measure of growth quickly becomes a fundamental shift in how a bank operates, earns revenue, and manages risk.
However, this landmark also brings substantial regulatory and compliance obligations, including changes to debit card revenue streams, mandatory participation in annual stress tests, and enhanced infrastructure requirements.
It’s no surprise, then, that banks approaching the $10 billion inflection point often face a new level of uncertainty as their business model begins to evolve.
In a recent PaymentsJournal podcast, Ellen Davitt-Lalwani, Senior Director of Portfolio Advisory Services at Fiserv, and Brian Riley, Director of Credit and Co-Head of Payments at Javelin Strategy & Research, addressed commonly asked questions about this transition and outlined the leadership, compliance, risk management, and card program strategies that can help ensure a smooth crossover.
The Regulatory Uptick
One of the most impactful aspects of the transition is the requirement to comply with debit interchange regulations under Regulation II, introduced through the Durbin Amendment to the Dodd-Frank Wall Street Reform and Consumer Protection Act.

While these rules were passed to strengthen the U.S. financial services system following the 2008 financial crisis, the card-driven payments landscape means they also carry revenue implications for banks crossing the $10 billion threshold.
“Cards are your customers’ primary physical contact with your brand,” Davitt-Lalwani said. “We need to remember that as Regulation II is put into place—as an institution moves from unregulated to regulated—their interchange can be cut by 40% or more and every transaction matters, for both debit and for credit. Interchange cuts also affect consumer and business debit transactions. For some clients, their interchange ranges from 30% to 50% of non-interest income today.”
Indeed, the impact stems from the Regulation interchange cap: $0.21 per transaction, plus five basis points of the transaction amount, and an additional $0.01 for fraud prevention. This is significantly lower than what many midsized institutions currently earn, making it essential to accurately estimate the resulting interchange revenue gap, particularly on debit transactions.
While this is one of the most consequential changes, it is far from the only compliance consideration.
“One of the things that comes into play is Dodd-Frank stress testing, which puts a highlight on bank liquidity and, since you have become a large institution, ensures that you have the wherewithal to survive changes in the economy,” Riley said. “There are other regulations that also come into play that affect revenue, and there are higher compliance costs that come through the Volcker rule, which has to do with investments in private equity and financials in the background.”
Preparing for What’s Ahead
Given these new obligations, banks often have several key questions as they prepare to cross the $10 billion milestone. For example, institutions frequently ask whether they should proactively communicate with regulators and third-party providers about their trajectory.
“That is certainly a ‘yes,’” Davitt-Lalwani said. “In terms of working with prudential regulators as well as third parties, having at least six months advance notice is a good idea. In terms of regulators, feel free to reach out to the Ombudsman’s office. It’s a good opportunity for your financial institution to establish a relationship with your regulator and it gets you off on the right foot.”
“In terms of reaching out to third parties such as Fiserv, Visa, and Mastercard, there is typically an orchestration of operations and technology that needs to take place,” she said. “That six months advance notice gives everyone an opportunity to circle the wagons and put all of the right components in so that when you’re truly ready to step across that threshold, you’re doing it with all parties fully knowledgeable.”
Another common question is whether additional asset thresholds trigger further regulatory requirements. The answer is yes. The $25 billion threshold introduces another layer of complexity, often compounded by the fact that it’s frequently reached through mergers or acquisitions.
As banks near $10 billion in assets, some consider temporarily slowing growth until the necessary infrastructure is in place. This can be supported through deposit management partners such as StoneCastle, which can help move deposits off balance sheet until the institution is ready for the crossover.
However, these partnerships must be established well in advance. Beyond balance sheet management, they also provide a buffer against “flights to safety,” when volatile market conditions drive sudden surges in deposits.
“I’ve been through that $10 billion inflection point and one of the financial institutions that I was employed by experienced that flight to safety just as we were approaching the $10 billion mark, and it pushed us right up over the threshold,” Davitt-Lalwani said. “We are a nation that has a very dynamic socioeconomic market, so preparation is the better part of valor in this. I strongly recommend that financial institutions consider putting those types of tools into place.”
A Regulator in Residence
Preparation also requires a clear understanding of more complex reporting expectations, including enhanced audit, compliance, and risk reporting that often demands new data capabilities.
In some cases, banks should also be prepared for the possibility of an on-site regulatory presence.
“There could potentially be a regulator on-site all day every day with your associates—whether it’s in the cafeteria, walking through the parking lot, or in the elevator,” Davitt-Lalwani said. “They’re going to be able to pick up on conversations and to see and hear things that may not have occurred in prior situations. They’re important components as to how financial institutions need to be prepared and how they can work for success in the future.”
These expanding obligations frequently require investment in both staff and technology. As teams grow—often in unanticipated ways—strong organizational alignment and clear communication becomes critical.
Just as important is maintaining a customer-centric focus. As institutions scale, they can lose the personal touch that differentiates them. Structured feedback mechanisms, such as customer surveys, can help preserve that connection during the transition.
“One of the best customer surveys I’ve ever had was to ask our customers if there was one thing they could change in the near term that would improve their relationship with us, what would that be?” Davitt-Lalwani said. “Your customers and members will tell you where you need to improve so they can willingly work with you and deepen their relationship.”
“On the back end of it, make sure to communicate to your customers or your members that we’re listening to you; we’re hearing what you have to say, and this is how we’re responding to meet your needs,” she said.
Balancing Growth and Risk
Amid these changes, banks must continuously balance revenue generation with enterprise risk management. While the transition can feel complex, the ultimate goal is to position a successful institution for sustained growth.
“You don’t end up at this threshold by accident,” Riley said. “You either got here through organic growth or through a merger. The focus is on the prep work, having everything in place because this is not a casual move and it needs planning that goes in front of it. Life will change when you crossover that barrier. The opportunities are certainly there and the risk is also there.”
Given these considerations, establishing a comprehensive communication strategy ahead of the $10 billion threshold is essential—not just to explain new processes, but also to prevent internal silos or unintended organizational friction.
“You want to make sure that everyone understands that higher water raises all boats,” Davitt-Lalwani said. “It’s important that we fortify the organization in all of the appropriate places Regulators, talk to your associates at the front-line level, at the back-office level, as well as executive and mid-management. (You want to make sure they) have an understanding as to how and why the organization is changing and what the anticipated needs will be.”
“Communication is key, but it can be elusive, so having the board and the executive team devise a plan and putting in listening posts to make sure that the message is getting out there is a great thing to do and should not be overlooked as you embark upon this journey,” she said.
[contact-form-7]The post Inside Banking’s $10 Billion Inflection Point appeared first on PaymentsJournal.
14 May 2026, 1:00 pm - 26 minutes 33 secondsThe Hidden Cost of Fraud Disputes Is Hitting Banks Hard

Fraud disputes are one of the fastest ways for banks to lose customers—and one of the least prioritized parts of the business. Despite the high costs, many institutions still treat them as a back-office function rather than a decisive point in the customer relationship.
Beyond immediate losses—such as chargebacks, write-offs, and investigation expenses—banks also lose revenue when an engaged customer no longer keeps their account top of wallet.
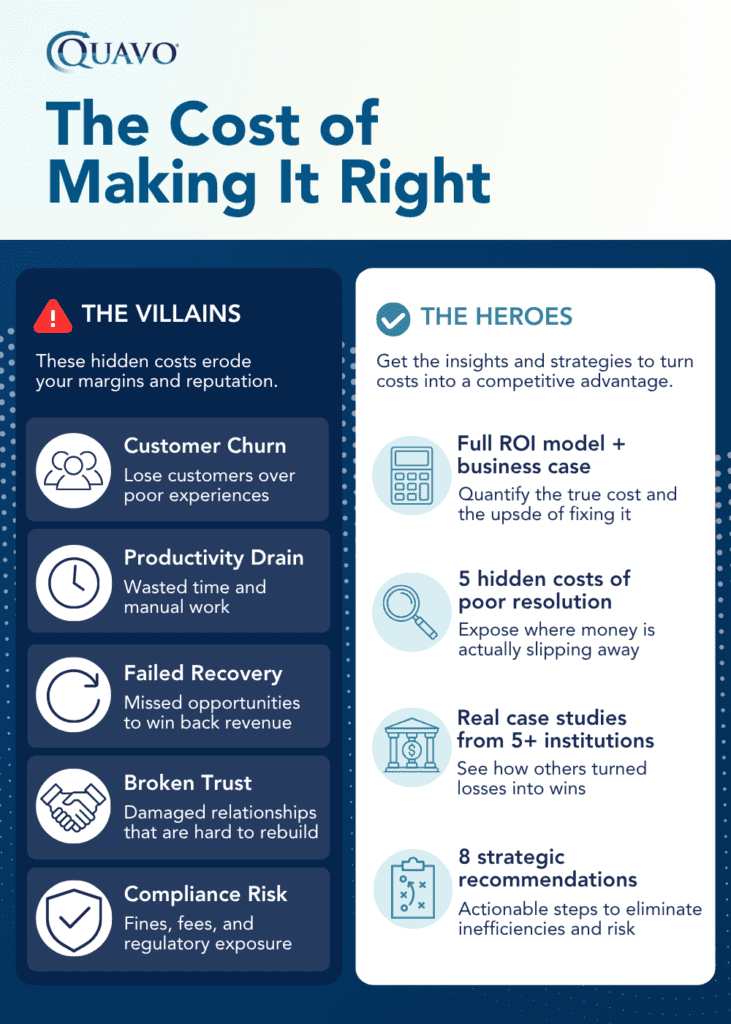
In a PaymentsJournal Podcast, Steve Durney, Vice President of Partnerships and Alliances at Quavo, and Suzanne Sando, Fraud Analyst at Javelin Strategy & Research, discussed the hidden costs of fraud disputes. It’s a problem that will only intensify as AI and agentic commerce evolve.
Customers Are Willing to Move On
Banking industry recovery rates for fraud average around 64%, leaving more than a third of disputed dollars unrecovered. For most banks, disputes are an expensive process, with operating costs eroding already thin margins.
Research suggests that if a fraud issue or dispute isn’t handled effectively, 60% to 70% of customers will move to another bank. Notably, the outcome doesn’t always have to favor the customer, as long as the process is managed transparently and resolved efficiently.
Once customers feel they aren’t being treated fairly, it’s difficult to restore trust. Accounts may be quietly abandoned, and products go unused. Even without formally closing an account, customers often disengage entirely.
“We’re seeing growing numbers of consumers who are willing to close an account and walk away when they have a bad experience with their account,” said Sando. “Setting everything back up with a whole new financial institution—like bill pay or getting all your accounts linked to whatever other financial accounts you were linked to—it’s a tremendous hassle. If you’re willing to go through all of that, that says a lot for how important security and customer service is throughout a process like this.”
Modernizing the Dispute Process
Several aspects of the dispute process need modernization to improve efficiency and recover lost value. Because dispute teams rarely receive priority budget allocation, banks often underinvest in technologies that could significantly improve performance.
Organizations that ignore these inefficiencies and continue to deprioritize back-office enhancements only prolong the problem. Five years from now, they are likely to be facing the same challenges.
“The inefficiency really comes into what historically would have been categorized as judgement—something where a human being has to give opinion on in order to route it properly,” said Durney. “Second is the document interpretation, for documents that are incoming from either a consumer or a merchant, or being transmitted from the bank to the merchant. That’s the lion’s share of the inefficiency.”
Banks without standardized documentation and clear rules force teams to spend valuable time interpreting procedures instead of executing them. When deeper, manual investigations are required, staff should be freed from repetitive administrative tasks so they can focus on higher-value work.
Fighting Against Constant Turnover
High turnover within fraud teams is another persistent challenge, especially given the long ramp-up time required for investigators to become effective.
“I asked a bank not long ago, ‘What’s the turnover rate in your department and how long does it take you to onboard somebody?’” said Durney. “They said the onboarding was about six to seven months before they were effective, and they had a turnover rate of roughly 25%.
“If you’re turning over your staff every four years and it takes you six to nine months to have somebody be a top performer, that’s a radical impact on all these day-to-day manual tasks,” he said. “There has to be a way to get people up to speed faster, handling the cases in such a way that you can actually hold on to staff and you don’t have that turnover.”
Involving experienced compliance and regulatory professionals in designing dispute process technology can help reduce risk and ensure systems are better equipped to handle complex scenarios.
The Risks of Agentic Commerce
While banks are still working to modernize dispute processes and stabilize fraud teams, the next wave of change is already emerging.
Agentic commerce promises new opportunities, but also introduces significant fraud risks. When AI agents act on behalf of consumers, traditional fraud signals—such as behavioral biometrics, device intelligence, and IP address—become less reliable, making it harder to distinguish legitimate activity.
Fraudsters will increasingly leverage agentic AI in ways that are difficult to predict.
“Once people really figure out how to use the tools to be able to make the agents go off and do things, you’re going to get the gray area of people abusing the system,” said Durney. “The use cases that we see so far are using AI to navigate the system. Say: ‘I bank with Bank X, tell me how to navigate the disputes process,’ and it will generally give you a pretty good recipe as to how to get through it.”
Banks are already anticipating how AI could go wrong. Those looking to stay ahead in fraud dispute management must prepare now.
“HBO’s Silicon Valley has a perfect example of this,” Durney said. “They told the AI to go buy them burgers for lunch, and then a pallet of frozen hamburgers showed up. Did the AI do what it was supposed to do? More importantly, what is a consumer going to do? A consumer is going to find the easiest path to go. I need somebody to be my advocate to fix this problem because I didn’t want a pallet of frozen hamburgers.”
[contact-form-7]The post The Hidden Cost of Fraud Disputes Is Hitting Banks Hard appeared first on PaymentsJournal.
13 May 2026, 1:00 pm - 24 minutes 51 secondsCrypto Payments Are Ready for the Mainstream

Cross-border payments have long been defined by delays, fees, and a maze of intermediary banks. Stablecoins are changing that—offering a faster, simpler alternative that cuts out the middleman entirely.
This use case is one of the key drivers behind the stablecoin market’s rapid growth in recent years. However, stablecoins—and digital assets more broadly—have the potential to reshape virtually every payment scenario, from enterprise transactions to retail purchases.
In many cases, the infrastructure to support these applications is already in place, largely due to the rapid proliferation of crypto payment gateways. While early iterations did little more than add a ‘Pay with Crypto’ button at checkout, these crypto gateways have quickly evolved into full-scale payments orchestration platforms.
In a recent PaymentsJournal podcast, Kate Lifshits, CEO of NOWPayments, and James Wester, Director of Cryptocurrency and Co-Head of Payments at Javelin Strategy & Research, discussed the dynamic powers of stablecoins, the remaining regulatory and infrastructure challenges, and how the final barriers to mainstream adoption are steadily falling.
Solving Pain Points
Although they aren’t issued by the U.S. Federal Reserve, leading stablecoins have effectively become a digital representation of the dollar. This makes them a powerful alternative to the existing rails.
“There are some pain points that most merchants that use traditional rails face,” Lifshits said. “Those are speed, availability, costs, and the inability of the traditional rails to meet the rising demand for optimization and innovation. That’s exactly where stablecoins come in because if we’re talking about speed, we are talking about several seconds instead of several days. If we’re talking about costs, we’re talking about several cents or a dollar instead of a lot of dollars.”
Beyond efficiency gains, the modern infrastructure supporting stablecoins can serve as a springboard for innovation. From a liquidity perspective, near-real-time settlement enhances the time value of money, enabling organizations and consumers to deploy funds more effectively.
Together, these advantages make stablecoins a compelling option across a wide range of use cases.
“In the way that business-to-business payments are being looked at, it is just having another option,” Wester said. “For the longest time there were no options in how you paid your bills, or the options you had were limited, expensive, and slow. It’s just having a new rail that has cheaper, faster, and better settlement time and removes some of the intermediaries who are taking a toll to move things along. And there are also friction points in having all of those intermediaries.”
“We’re creating a whole new option that didn’t exist before, especially from a B2B standpoint,” he said. “Even remittances—when you’re talking about consumers paying each other across borders—what you’re seeing now is a new option that is cheaper, faster, better, and begins to drive down costs everywhere.”
The Added Bonus of Crypto
For all the progress in crypto payments, onboarding remains a sticking point. Many merchants are still wary of the perceived complexity of integration, while others lack a clear starting point.
“It’s up to the crypto payment gateways to give them the easiest onboarding flow ever,” Lifshits said. “That would mean that when they start using the payment gateway, they see all the traditional tools they are used to, but with the added bonus of crypto.”
The goal is to make crypto payment gateways as intuitive and seamless as the tools merchants already use, such as those offered by Stripe or PayPal.
Gateways must also address longstanding concerns around crypto acceptance, namely, how digital assets are managed after receipt and the volatility of cryptocurrencies like bitcoin and Ethereum.
This makes it critical for merchants to have the ability to convert crypto to fiat at any point, as well as the flexibility to choose how actively they manage digital assets. This optionality helps address another concern: crypto transactions can be unforgiving. For example, sending funds to the wrong wallet can have irreversible consequences.
While the infrastructure to mitigate these risks has improved greatly, silos still exist. Many organizations continue to rely on separate payment stacks for traditional rails and digital assets.
“We’re seeing development along both of those,” Wester said. “There are some nuances to payments the traditional way that we haven’t built into stablecoins yet. But what’s surprising to me is how quickly we are identifying those nuances, how quickly we are beginning to see the traditional rails and the legacy providers look at stablecoins and say, ‘We can do that, we can integrate that, let’s bring that into more traditional bank and financial institution payment rails.’”
Advancing the Crypto Mission
Rising institutional interest is driving new regulatory measures worldwide. These landmark frameworks represent a turning point for an industry rooted in decentralization and long viewed with skepticism by global financial leaders.
“Regulation always lags innovation. You have an innovation, you don’t know what that innovation is going to entail, so regulators don’t exactly know what they’re supposed to be regulating,” Wester said. “Now that we’re seeing that it does provide cheaper rails, faster clearing, and all sorts of innovation, traditional financial services began to say to regulators: ‘We want to be able to do this,’ and regulators finally started coming around and saying, ‘Let’s see what we can do.’”
Recent efforts include Europe’s Markets in Crypto-Assets (MiCA) framework and the GENIUS Act in the U.S.—developments that would have seemed implausible just a few years ago. Yet digital assets are proving they can be as compliant, safe, and secure as traditional financial instruments.
They can also align with existing Know Your Customer (KYC), Know Your Business (KYC), and anti-money laundering standards. In some respects, blockchain-based transactions offer even greater transparency than traditional systems.
As these long-awaited regulations take effect, it is critical for digital asset firms to embrace and adhere to them.
“To further the mission of crypto, a payment gateway should be licensed, they should understand each country’s rules, and help businesses to operate with crypto on a regulated and licensed and compliant basis,” Lifshits said. “That would mean not just licenses, but also procedures as KYC and KYB. But here we see an interesting challenge—the KYC and KYB procedures should be out there without breaking the UX.”
“That’s where the conversion usually starts to fail, when businesses are trying to be compliant and safe, but then the UX suffers for it,” she said. “It’s up to the payment gateway to comply with the rules, but to still to be able to provide a better experience than the traditional payment gateway that only works with fiat.”
The Future Is Now
Delivering a strong user experience while maintaining compliance is a difficult balance, but a crucial one. Many users remain hesitant to engage with crypto payments, making trust a decisive factor.
“You can integrate this into consumer payments, remittances, commercial payments—whatever application it is,” Wester said. “It’s all a part of simplifying that user experience and then educating people on just how simple it is.”
Ultimately, ongoing improvements in infrastructure, compliance, and education are all aimed at building that trust—the foundation for mainstream adoption of crypto payments.
“If crypto itself is getting more trust, the same should go for crypto payment gateways,” Lifshits said. “And it’s not just education. There should also be a bit of marketing here because crypto is already here.”
“It’s not just something in the future, it’s here. And you should do it now because while you’re waiting, others are already reaping the benefits,” she said.
The post Crypto Payments Are Ready for the Mainstream appeared first on PaymentsJournal.
12 May 2026, 1:00 pm - 18 minutes 1 secondThe Passkey You Can’t Steal: Why Hardware Beats Software for High-Stakes Authentication

Today is World Passkey Day. And while the industry celebrates the shift away from passwords, the more important question is what kind of passkey replaces them. Many organizations recognize that passwords are on the way out, with passkeys emerging as a replacement. What’s less widely understood is that the two main types of passkeys—synced and hardware-bound—serve very different use cases and carry distinct risk profiles. While both improve security and usability compared to passwords, one offers much greater protection.
In a Payments Journal Podcast, Adam Lowe, Chief Product and Innovation Officer at CompoSecure and Arculus, and Tracy Goldberg, Director of Cybersecurity at Javelin Strategy & Research, broke down how these approaches differ in practice. They explored how keys behave when stored in software versus hardware, and why those distinctions are especially important in payment authentication.
What Is a Passkey?
A passkey is a cryptographic credential that allows a user to authenticate their identity with an application or service without a password. Many consumers encounter passkeys through mobile devices or platforms like Microsoft, often using biometrics such as fingerprints or facial recognition to log in.
In most of these cases, the underlying credentials are software-based and synced through the cloud. This approach is very convenient: a single passkey can work seamlessly across multiple devices. However, that convenience introduces risk. If a user’s cloud account is breached, the bad actor may gain access to synced credentials, creating a significant security concern.
Synced passkeys also face additional challenges. For example, while modern implementations are designed to resist replay attacks, improperly implemented systems or surrounding infrastructure can still be vulnerable if intercepted authentication data is reused to trick a system into granting access.
“The more we have out there that’s living in the cloud, it’s just more readily accessible to cybercriminals,” said Goldberg. “The more that we can do in a physical environment—in addition to what we’re doing in a digital space—just enhances the security.”
As Goldberg noted, hardware-bound passkeys are generated, stored, and managed on a local device, like a smart card or USB. These are widely used in high-security environments, including U.S. government and intelligence settings, and are generally considered best-in-class for strong authentication.
“Software passkeys are great for that first layer, but we really need that depth of defense,” said Lowe. “Adding hardware local passkeys provides that next layer of defense for users.”
A common misstep that organizations make is adopting hardware passkeys without fully modernizing their underlying systems. Often, this is done to avoid disrupting user workflows. While hardware passkeys can add a strong layer of protection, their benefits are limited if they are simply layered on top of legacy infrastructure rather than integrated into a modern authentication architecture.
“When you sign, you’re getting a digital signature from the key, but you’re also attesting,” said Lowe. “There’s a certificate on hardware that proves it’s a valid hardware signer. While that food chain lives in the cloud, it can be manipulated. So another value to the hardware is not only am I signing, I am signing from a valid piece of hardware in a very straightforward way.”
Non-Portability Is the Key
With hardware-bound passkeys, credentials are generated and stored within a secure element on the device. A secure element is a specialized chip designed to create and protect cryptographic keys—similar to those used in passports or payment cards.
The defining characteristic here is non-portability. The private key never leaves the device. This is analogous to keeping a physical house key in your pocket: access requires possession. Because the key can’t be exported, duplicated, or remotely accessed, the attack surface is dramatically reduced.
“We’re not saying that software passkeys go away,” said Goldberg. “It’s just an additional layer, a step-up authentication. It’s going to take a little bit more friction to authenticate and verify certain types of transactions or even certain types of individuals.”
Read Privileges vs. Write Privileges
So when are software passkeys good enough, and when is hardware-backed authentication necessary? One useful way to frame the distinction is through read versus write privileges.
Read privileges—access to view data—generally carry lower risk, since no changes can be made. In these scenarios, software-based passkeys may provide an acceptable balance of security and convenience. Write privileges, on the other hand, allow users to take actions that alter systems or move value, such as initiating payments. These higher-risk operations are where hardware-backed authentication becomes far more important.
“That’s where we typically see that software to hardware migration, for stepping up an event,” Lowe said. “A very typical example would be sending a wire, sending any reasonable amount of money. Any time you get a risk flag, you can have the user tap into a step-up event.”
The Tipping Point
The shift to hardware-bound passkeys could have occurred years ago, but widespread adoption likely depends on a tipping point—one that convinces organizations the added security justifies the change.
“That tipping point is going to be a combination of increased cybersecurity risk, such as network infiltration that leads to data breaches,” said Goldberg. “It’s going to be upticks in fraud and increased risk to identity.”
Many experts expect that payment flows, in particular, will increasingly require hardware-based authentication, given the high value and sensitivity involved.
“If you do hardware-based authentication on a payment card, it shows possession of the physical card, which also answers so many fraud questions,” Lowe said.
“We’ll get to the tipping point where consumers are concerned about their identities being compromised, and governments have more concern about verifying the authenticity of individuals, agents, and companies,” he said. “The whole notion of getting away from software-based authentication to having this additional layer of hardware will just become second nature.”
The post The Passkey You Can’t Steal: Why Hardware Beats Software for High-Stakes Authentication appeared first on PaymentsJournal.
7 May 2026, 1:00 pm - 18 minutes 34 secondsTips on a Prepaid Card: A Practical Solution with Broad Industry Impacts

When events like the NCAA Final Four come to town, they bring an influx of short-term workers who keep everything running—but often for just four or five days. Despite the brief duration of this work, many organizations still rely on traditional payroll systems to compensate them, creating unnecessary friction where speed and simplicity matter most.
In industries that have relied heavily on cash tipping, such as hospitality, prepaid cards can be just as game changing. Instead of asking for a valet driver’s Venmo, a diner could scan a QR code and send a tip directly to the driver’s prepaid account.
While event staffing and tipping are two clear examples, the potential extends much further. In a recent PaymentsJournal podcast, Ben Osmond, SVP of Treasury and Payment Solutions at U.S. Bank, and Jordan Hirschfield, Director of Prepaid at Javelin Strategy & Research, explored the impact of prepaid solutions across sectors such as the gig economy and contract work.
As cash and checks continue to decline, prepaid products can reshape the work experience for contract and seasonal workers, while also delivering benefits for employers.
Filling the Tip Card
As tip jars have gone increasingly cashless, restaurants have sought more efficient ways to distribute tips digitally.
“What they are doing is using prepaid programs to provide tips at the end of shift,” Osmond said. “There’s some interconnectivity with the point-of-sale systems where we’re able to calculate the tips that a server is going to receive so that they can have those loaded onto a prepaid card at end of shift. Often, they will have them on their card and in their account before they jump in their car or jump on the bus to head home.”
This model is often well received, in part due to consumers’ familiarity with gift cards and the stored-value accounts like those offered by Starbucks or Target. That said, some workers may still hesitate to accept tips through what they perceive as a gift card format.
“Sometimes people don’t understand that you still get a regular paycheck maybe from your hourly work, and that a card that you get for your tip outs is a payroll card,” Hirschfield said. “Some of that is just the messaging and the idea around it, where they don’t think of it as payroll but as their tip card, that’s what it’s there for and that’s the intent.”
“It’s a payment option; it doesn’t mean it’s the one thing they will get,” he said. “When you go home at the end of the day, you’ve got that tip money in your hands in the same way you would have in a cash environment. These products support the whole idea that there’s multiple ways to pay people, just like they’re always have been. It used to be you would get your check for your hourly work and your cash for your tip outs. Now, we’re moving to a digital environment for that.”
Winning or Losing Talent
Beyond tipping, digital prepaid cards can dramatically improve the work experience for contract and seasonal workers across industries.
“Instant issuance changes the game when you think about those contractors, those seasonal workers and short-term employees whose entire employment experience might come down to five days of working at an event,” Hirschfield said. “When they finish on the day it closes, pay them out and their entire experience is complete. They’ve worked their hours; they’ve received their payment, and everyone has a clean break.”
This streamlined approach creates a win-win: payers benefit from simplified coordination, while workers receive fast, secure, and flexible compensation.
As short-cycle payments become more common—whether for summer jobs, event staffing, or project-based work—prepaid cards are well positioned to meet this important need.
“More employers are starting to realize the value because today’s workforce is mixed,” Osmond said. “There are gig employees, contractors, and temps, and a lot of the legacy payroll systems struggle with high turnover and rapid onboarding of employees. Ultimately, a pay experience can win or lose talent in a tight labor market. It’s very important that employees are being paid the way that they want to be paid.”
Real-Time Earnings Access
Just as important as how workers are paid is when they are paid. In a digital payments landscape, where consumers can receive near real-time transfers via apps like Zelle, the answer is increasingly immediate.
“One of the most relevant trends today is earned wage access, the ability for an employee to receive wages for hours that they have already worked but have not yet received a paycheck for,” Osmond said. “With that Friday or every other Friday payday, they’re able to access these funds early and request a portion of their wages which can be sent to them electronically onto a prepaid card, plastic or digital.”
Regardless of how payments are delivered, workers expect digital access to their financial information. This makes it critical to offer a robust app that provides full visibility into balances, transactions, and spending. This is especially important for contract and short-term workers, many of whom juggle multiple jobs and remain constrained by traditional pay cycles.
“Having these options where you can get paid either with earned wage access on an early basis or a couple days early, those are critically important to the people receiving that money—especially when they may need to spend that money as soon as they earn it to fit their lifestyle.” Hirschfield said. “Also, you get people who are potentially underbanked and unbanked, and this can also fill that gap.”
From the Employer’s Perspective
While the benefits for workers are substantial, employers also stand to gain. Paying via prepaid can reduce onboarding time and administrative costs, enabling workers to get started more quickly.
“It can cut costs around eliminating checks or email reissuing of checks, things of that nature,” Osmond said. “It can reduce fraud. That’s something that often doesn’t get talked about from an employer’s perspective, but there is fraud on paychecks. They’re also having less calls and less concerns into their HR or their payroll department with questions about their checks.”
“You can lower the cost of ownership scale of all of these things,” he said. “We work with a lot of quick-service restaurants that have many different locations that are using our prepaid products. By having one product and one disbursement method, they’re able to be much more efficient than they would by delivering checks to each different location.”
Immediate payouts can also play a valuable role during employee separations. Whether voluntary or involuntary, issuing final wages via prepaid card can help defuse what is often a sensitive and time-critical situation.
And these scenarios are only part of the broader opportunity for prepaid solutions within the full-time workforce.
“You look at other things where it might be an off-cycle payment, where it could be a bonus or sales incentive program,” Hirschfield said. “These things are done off cycle; they’re instantly done. You hit an incentive bonus on sales, you’re paid instantly, and you feel rewarded. These are all examples that play into why having programs like this help.”
A Frontline Experience
Taken together, these developments position prepaid cards as a valuable part of modern work experience—and signal the potential for disruption within the broader payroll space.
“As we think about this as a whole, payroll and wages aren’t just a back-office function anymore, it’s a frontline experience,” Osmond said. “Payroll cards and wage cards have moved beyond check replacement to become a digital infrastructure for the workforce that today is mobile, it’s mixed, and it’s often outside of traditional banking.”
“The next standard is simple, it’s a quick onboarding process,’ he said. “We need to pay people fast, we need to pay them consistently and we need to do it with controls in place that employers can stand behind. What these products do, it helps make a real bank-issued program that can support earned wage access as well as tip functions—without changing the payroll cycle as a whole for the employers.”
The post Tips on a Prepaid Card: A Practical Solution with Broad Industry Impacts appeared first on PaymentsJournal.
29 April 2026, 1:00 pm - 31 minutes 16 secondsAs Fraud and Agentic Risks Mount, Data Provides Continuity

Not long ago, fraud teams could keep pace by reviewing incidents one by one. That era is ending. Armed with artificial intelligence and cloud-scale infrastructure, today’s cybercriminals operate faster, more broadly, and with far greater sophistication than ever before.
The rise of agentic commerce will only intensify these challenges, in part because it upends a longstanding assumption in fraud prevention: that bot traffic is inherently suspicious. In a world where legitimate transactions may be initiated by AI agents, that distinction becomes far less clear.
In a recent PaymentsJournal podcast, AtData’s Diarmuid Thoma, Head of Fraud and Data Strategy, and Brandt Hoffman, Sales Director, Fraud Services, along with Jennifer Pitt, Senior Fraud Management Analyst at Javelin Strategy & Research, discussed how these shifts are dramatically impacting payments risk.
At the center of this transformation is a simple but growing imperative—organizations must know, with confidence, who (or what) is on the other end of every transaction. Achieving this now requires systems capable of analyzing and contextualizing vast, dynamic data streams in real time.
The Outputs of Scalability
Historically, many fraud attacks were treated as isolated events, leading financial institutions to adopt a reactive, situational approach. However, there are often patterns that emerge when these incidents are viewed collectively. Recognizing and operationalizing those patterns is critical.
“From a law enforcement perspective, I remember a mail theft case that I investigated,” Pitt said. “We conducted a search warrant on the suspect’s home and found bags of open and unopened mail. We also found stacks of paper that contained full personally identifiable information—name, date of birth, Social Security number, next of kin, last known addresses—you name it, he had it.”
“We searched his phone and his computer, and we were able to see that he was connected with several other suspects that we were already investigating,” she said. “What we uncovered was this hierarchical organized crime ring where there ended up being more sophisticated identity theft and other crimes. If we were just looking at one of those players or incidents, we wouldn’t have seen this whole organized crime ring.”
While traditional vectors like mail fraud persist, the digital landscape has allowed bad actors to expand their reach exponentially. Technologies such as AI and cloud computing have supercharged criminal capabilities faster than most organizations can evolve their defenses.
Beyond just deploying generative AI to create more convincing impostor sites and deepfakes, bad actors can now deploy AI agents to autonomously carry out widescale fraud campaigns. For example, agentic AI has been used in a technique where email addresses are rapidly and sequentially created for use in fraudulent activities.
“We see thousands and thousands of them every day, where we see sequential types of emails created and they’re not necessarily in one client,’” Thoma said. “Somebody’s using an email over here to create a bank account and going and buying a pair of sneakers over there.”
“Individually, it looks fine; there’s nothing wrong there,” he said. “At a platform level, we see the cumulative effect. It’s a simplistic example, but that type of behavior is a direct output of the scalability of fraud.”
Distinguishing Malicious Automation
Given agentic AI’s potential to amplify fraud across every channel, the emergence of agentic commerce presents unique challenges for fraud prevention teams.
Many of the open questions around agentic transactions center on authorization. In the conventional e-commerce model, the shopper selects items, completes verification, and explicitly authorizes the purchase. When an AI agent acts as the consumer’s proxy, however, new gray areas emerge.
“What happens in a chargeback scenario?” Thoma said. “The industry hasn’t got all the answers on that. It’ll slowly emerge, but one of the things that won’t change is history. It’s still you buying it. Especially for physical goods, it’s going to your physical location, it’s going to your name, and it’s probably using your e-mail address to confirm all the details. There’s still a lot of information, even in the agentic world, that’s going to be coming through.”
This means that one of the most important considerations for fraud prevention will be the user’s history. Fortunately, this data is already present for many consumers. For example, the organization can confirm the age of an email address, whether it has been actively used, and if there are any red flags associated with it.
This historical data becomes a critical point of continuity as organizations design fraud strategies for agentic commerce.
“It was always, ‘Let’s look at the negative aspects of what this transaction could present,’” Hoffman said. “Now, we have to be cognizant to bring in those positive signals. What are the good signals that we can lean on? What allows us to interpret or infer more quickly? How do we start to identify what it means to be a positive bot, or to be a good transaction along the line?”
A Timeline Event
To act on these signals effectively, teams must start from an accurate baseline. A core lesson from AI is that models are only as strong as the data that feeds them. Just as importantly, that data must remain current, especially as consumers’ digital footprints continue to expand.
“Many still look at data like it’s a credit report, where it’s a static thing that you see in a piece of paper and that’s it,” Thoma said. “It’s not. It’s a timeline event. If you think about when you were 20 to now, you’ve had different addresses, you’ve had different IPs and different devices. Your name may have changed for different reasons, and your email probably changed one or two times.”
“Your profile naturally evolves, so the importance of the data quality and the skill in the overlaying models is to know when that change is abnormal versus normal,” he said.
A practical way to evaluate changes in a user profile is through percentage-based shifts. Significant or rapid deviations across key attributes may indicate potential account compromise.
Similarly, the repeated use of a single element across multiple account creation attempts can signal synthetic identity activity, where bad actors combine real and fabricated information.
“We commonly see that, and its behavior that is distinctly different from somebody who’s just moved addresses,” Thoma said. “Yes, they’ve moved addresses, but a lot of the time when people move, they only move a couple of blocks down. There’s continuity in that profile, where we can still say that even though the profile has changed, it’s still fine.”
“That’s a broad example of how important it is to have that data quality,” he said. “Because if you don’t have fresh data to reference, the timeline to reference back further, you can’t say, ‘This is normal behavior for them or not.’ That’s how important it is.”
Data for the Whole Organization
The growing emphasis on identity verification is driving a widescale shift in how financial institutions approach fraud prevention. Yet opportunities remain to break down data siloes and improve visibility across systems.
“We are seeing some evolution in the ability for payments teams and fraud teams to come together quicker,” Hoffman said. “Payments teams are very focused on the transaction and what it means to bring that revenue in. There still is some hesitation for the fraud teams and the payments teams to merge together.”
“In the most advanced organizations that I work with, those two functions are working hand-in-hand,” he said. “They know exactly what’s going on from a payments perspective and how that affects the flow of fraud.”
The pace and complexity of the threat landscape demand more sophisticated infrastructure. Modern fraud prevention solutions rely on graph-based methods to map relationships between entities—sometimes referred to as fraud topology or halos.
These topology-aware systems can enhance detection accuracy while reducing costly false positives. They also enable organizations to apply the right level of friction within the customer journey, including step-up authentication when warranted.
While designed for fraud prevention, the benefits of these capabilities often extend well beyond risk teams, strengthening decision-making and operational efficiency across the entire organization.
“The data is customer data; it has huge amounts of value,” Thoma said. “You’re seeing their geolocation, behavior, age demographics—all that stuff is extremely important for the business, not just for the fraud team. Everybody thinks that’s a lot of money for fraud prevention, but it becomes very cheap because you’re splitting that into multiple budgets.”
“The marketing team can use it for targeted products, and you can increase conversions,” he said. “It doesn’t have to be fraud data, it’s company data for all divisions of that business to use.”
The post As Fraud and Agentic Risks Mount, Data Provides Continuity appeared first on PaymentsJournal.
23 April 2026, 1:00 pm - 21 minutes 56 secondsWhat Would it Take for Stablecoins to Replace Wire Transfers in B2B Payments?

International wires have long been the default for B2B payments—an entrenched system that works, but few would describe as optimal, given multi-day settlement timelines and high fees. But as stablecoins gain traction in cross-border transactions, businesses are starting to ask a more fundamental question: Can we replace wires altogether?
In a PaymentsJournal Podcast, Avinash Chidambaram, Founder and CEO of Cybrid, and James Wester, Co-Head of Payments at Javelin Strategy & Research, discussed what would need to happen for stablecoins to become the default mechanism for B2B payments. What’s exciting as well is the possibility of even more use cases across payments, treasury, and remittance. “There are all sorts of things you can do better that you don’t consider to be a problem,” Wester said. “But maybe with new technology, we can do things that you didn’t even know were possible.”
Structural Inefficiency
Wires work well enough—they move money from sender to recipient, which meets the core need. What most enterprises don’t see, though, is the complex web of systems and intermediaries behind these transactions; they simply build their processes around bank-based payments.
Over time, layers of intermediaries have made these systems deeply entrenched and difficult to replace. In the past, this made sense. Moving money across borders and oceans was a treacherous game, and paying a little extra for trust and security was a value-add rather than a painful cost. Now, however, times (and money movement) have changed. Organizations have access to tools that enable simpler, more streamlined alternatives with built-in trust.
“The inefficiency isn’t just technological, it’s structural,” said Chidambaram. “Whether it’s correspondent banks, clearing houses, processors, [or] compliance, these experiences that are happening in the background between banks cost both complexity and time, and are hugely inefficient.”
Looking for Improvement in B2B
Alongside new technology came new expectations of transparency; companies want to track their payment from the second it leaves their account to the moment it lands in a recipient account. However, this is simply not possible with wire transfers. Stablecoins, on the other hand, offer complete traceability—and enterprises are taking note. They can verify, often in near real time, that funds have been received. This visibility is driving growing interest as businesses see clear operational benefits.
“Most enterprises are focused on their core business and then they say, ‘OK, well, can I improve some of my operations and finance as a separate thing?’” said Chidambaram. “Now a customer can go into our platform and say I want to make a payment to this invoice and upload that invoice. We can automatically pull the funds from a customer’s account to fund the payment transaction, convert that to stablecoins automatically and then send stablecoin to the recipient’s wallet.”
“That can improve B2B payments from two contexts,” he continued. “First, it’s just faster. Secondly, you can see that it’s settled—that [your recipient] actually received the funds.”
Improving the User Experience
For the longest time, a major barrier to broader digital asset adoption, including stablecoins, has been poor user experience—complex interfaces and high stakes for errors.
Firms like Cybrid are beginning to address these challenges across retail, commercial, and enterprise payments. The experience now goes beyond accessing a wallet to include greater visibility into transaction status and fees.
The secret sauce is in programmability. Stablecoins by nature can be programmed—a payments team member can set up rules or triggers, which then guide how payments operate. For instance, payment terms. For instance, if you have to pay a supplier every month, you can create a programmable rule that ensures money lands on time, avoiding late fees or penalties and ensuring business continuity. But the use cases go beyond pre-determined rules and can become dynamic as well.“We’re starting to see people adopting ERP tools that have intelligence built into them,” said Chidambaram, “Where they can say, ‘Hey, your inventory is running low. Or you need to make these payments. Here are all the payables that you have.’ And over time, we’re finding that people are actually wanting to wait as late as possible to make those payments.”
Keeping Existing Workflows
Accounts payables and receivable teams already operate within established workflows in fiat currencies like the US dollar or Euro—for payroll, invoicing, and more—and are unlikely to overhaul them entirely. The good news, though, is that stablecoins operate in the background. When you make a payment, the recipient receives their local currency automatically (or stablecoins if they choose, but it’s not required). All the while, the business sending those payments benefits from speed, cost efficiency, and transparency.
“You’re going to have an organization that says: ‘This is how I do payroll for my local employees, but I need to do this other thing for my contractors overseas and this other thing for my suppliers,’” said Chidambaram. “Some of them might have taken only wires then, but are now accepting stablecoins. They have the ability to pick which rail makes the most sense to solve the problem.”
These benefits are especially relevant given the growing complexity of payroll, including irregular schedules and cross-border payments. Stablecoins could play a key role here. For example, enabling early wage access models that allow workers or suppliers to receive funds ahead of traditional pay cycles.
“You get paid every two weeks because, in our brains, that’s how you get paid,” said Wester. “That goes back to direct deposit, which goes back to you had to have a check, and that goes back to all sorts of things that go into the processes. Same thing with AR/AP and so many of our payment processes at the corporate level. Now we can rethink a lot of those things.”
Something Better
For the foreseeable future, stablecoins will coexist with traditional payment rails. Both are necessary to support the trillions of dollars moving through global systems today. But as enterprises, suppliers, and payers grow more comfortable, a larger share of that volume is likely to shift toward stablecoins.
“Many people think digital assets and stablecoins are a solution in search of a problem,” Wester said. “I’ll say, well, you know, what you’re doing now is slow, costly, and inefficient, with layers that you can’t see. You don’t think of this as a problem, but maybe that’s because you didn’t know there was anything better.”
A key remaining hurdle is integration. Stablecoin payments are not yet embedded in most enterprise software platforms, where traditional methods like wires are still the default. But as vendors evolve and enable easier integration, stablecoins will become more accessible—unlocking even broader use cases.
“Banks, PSPS, enterprises, large and small, every one of them have been thinking about stablecoins,” said Chidambaram. “How do I go in my take advantage of this? What are the capabilities I need? Then that starts to unlock people’s minds: What else can I solve with this new payment rail?”
The post What Would it Take for Stablecoins to Replace Wire Transfers in B2B Payments? appeared first on PaymentsJournal.
21 April 2026, 1:00 pm - 18 minutes 16 secondsInstant, Irrevocable Payments Demand a Fraud Prevention Reboot

When a shopper is tricked into making a fraudulent purchase, they expect recourse from their financial services provider. These guardrails are one of the reasons credit cards have become predominant in the U.S.—not only can consumers dispute charges after the fact, but many issuers proactively alert users when suspicious activity occurs.
Similar protections exist for ACH payments, but they are largely a function of the lag between payment initiation and settlement. With real-time payments, such as those facilitated by FedNow and the RTP network, this buffer disappears.
As both systems gain traction, particularly in B2B use cases, fraud prevention strategies must evolve to address payments that are instant and irreversible.
In a recent PaymentsJournal podcast, Darren Beyer, Chief Product Officer at Qolo, and Suzanne Sando, Lead Fraud Management Analyst at Javelin Strategy & Research, discussed how the convergence of faster payments and increasingly sophisticated fraud is fueling a full-scale redesign of fraud prevention architecture. It has also placed a demanding onus on financial institutions to implement highly precise risk controls while preserving the customer experience.
The Window Is Closing
As faster payments erode the traditional safety net around transactions, institutions must shift fraud detection to earlier stages of the payment process. In the past, organizations benefited from extended review periods, during which funds could be reversed if necessary. That capability is quickly becoming a thing of the past.

“In the world of instant payments, specifically around RTP and FedNow, you’ve got an instantaneous movement and settlement of money. And that’s where the problem lies, because there’s no longer time to pull this stuff back,” Beyer said. “There’s no window where you have an ability to say, ‘I really didn’t mean to send it’ or ‘I fat-fingered this particular account number.’”
“With that gone, it’s less of an opportunity for the people sending payments to fix problems, and that opens the window for fraudsters,” he said.
In this environment, striking the right balance between strong fraud prevention and a seamless customer experience is difficult, especially given the high expectations shaped by card and ACH transactions.
These challenges are accelerating the need for real-time decisioning, where firms analyze multiple data points to assess payment risk before processing. However, achieving high decision accuracy will likely require introducing some level of friction. While this may feel new in the context of real-time payments, methods like multi-factor authentication are already familiar to both banks and customers.
“Every time I log into YouTube, I get a six-digit one-time passcode,” Beyer said. “If I have to do that for YouTube, why is my financial institution not making me do that? They do when I log in, but if I’m doing a big payment out, shouldn’t the same thing be happening? Isn’t the ‘friction’ of getting a one-time passcode worth the extra two or three seconds it takes to put that into the website? I think the answer is yes.”
The challenge lies in applying the right amount of friction in an emerging payments model. This is where step-up authentication plays a key role. It allows institutions to adjust controls, enabling low-risk payments to proceed smoothly while subjecting higher-risk transactions to greater scrutiny.
Even so, introducing any friction into the customer journey can raise concerns for financial institutions.
“There has been an assumption that strong security will ruin the customer experience, but Javelin has found that good security can improve trust and adoption of certain payment channels and methods and new technologies,” Sando said. “Consumers and businesses want to know that their accounts and their money is protected and that they can trust the institution and the organizations that they choose to do business with.”
The Widening Technology Gap
Implementing safeguards that remain invisible to legitimate users yet highly effective against bad actors is no small feat, but the tools to optimize this balance are rapidly improving.
Artificial intelligence has been instrumental in advancing these capabilities, as it has across nearly every sector. However, many financial institutions have lagged in adopting these technologies.
“This is a scenario where it’s so rapidly changing the industry but the traditional players—processors and banks who are operating under a regulatory environment and are operating under an environment where you can’t inhibit people from getting access to their money—they have all these constraints,” Beyer said. “Fraudsters don’t, and they can just start playing with all these great new AI tools.”
“There’s always been a gap,” he said. “Fraudsters have always been ahead of the financial institutions and the processors, and the reason for that is they’re more nimble; they’re able to get things done quicker. If you didn’t have that gap, you wouldn’t have fraud.”
Unfortunately, this gap is not only persistent but widening. Rapid advancements in generative AI and the emergence of AI agents have enabled cybercriminals to scale both the speed and scope of their attacks.
“Bad actors can adopt those technologies quickly, and they’re incredibly creative. I don’t want to give them applause for that, but they’re incredibly inventive in the way that they take risks to use new technology,” Sando said. “It’s difficult for FIs to keep pace when it comes to the adoption of any innovation.”
“It’s no surprise that AI is a problem for criminal manipulation,” she said. “But we also know that it’s a huge asset for financial services that they could make great use of in terms of automating certain aspects of the customer experience. Or even the employee experience, for things that maybe used to be a manual review of transactions, or typical tasks that were completed during fraud investigations.”
Buttressing the System
AI has quickly become central to modern fraud defenses, given its ability to detect anomalies across massive datasets. However, the rise of real-time payments is fueling the demand for intelligent infrastructure that can function as an authentication layer within the payment flow.
This is especially critical in commercial environments, where overly restrictive controls can lead to false declines or delays—issues that can quickly escalate into serious operational and reputational damage.
Ultimately, faster payments are not just driving the need for better technology, they are forcing financial institutions to rethink their entire approach to fraud prevention.
“The organizations that are succeeding in instant payments are going to be the ones that can make the competent decisions on risk just as quickly as that money is moving in that real-time setting,” Sando said. “Fraud detection isn’t just this back-office function anymore, that just happens in the background without real knowledge of it. You have to highlight fraud detection because it’s now a critical piece of the payment experience.”
This shift in mindset is essential. The fraud threat is not going away, but institutions can take advantage of one constant: the pursuit of easy money often leads criminals down the path of least resistance.
“Fraudsters are always going to find a way, but they are fundamentally no different than anybody else in business,” Beyer said. “They have an ROI, their time is valuable, and they’re going to go where they can make the most out of their time. If your bank or your processor is tougher to get through than your neighbor’s bank or processor, they’re going to go to your neighbor.”
“Make your buttress, your fortress, your castle gate—all the armor that you’re going to put around your system. Make that better than your competition and they’re going to go to your competition,” he said. “You’re never going to get a 100% fraud-proof system. Fraudsters will always be ahead, but if you can make yourself better than the people around you, then you’re not going to be the target, they are.”
[contact-form-7]The post Instant, Irrevocable Payments Demand a Fraud Prevention Reboot appeared first on PaymentsJournal.
13 April 2026, 1:00 pm - 21 minutes 31 secondsFrom a Checkbox to a Differentiator: Redefining ACH Fraud Monitoring

Last year, the treasurer’s office in Warren County, New York sent $3.3 million to what it believed was the county’s roadwork and maintenance contractor. It was not—the payments were instead routed to a fraudulent account. Because the county had recently switched from paper checks to ACH, the treasurer’s office had no account verification policies in place to prevent what turned out to be a textbook case of fraud.
While the damage in Warren County represents the upper end of the spectrum, this incident is far from an outlier. It underscores the importance of implementing ACH protections, which many organizations already have in place. Too often, however, these measures are treated as a set-it-and-forget-it solution or merely a compliance checkbox.
In a recent PaymentsJournal podcast, John Gordon, CEO of ValidiFI, and Suzanne Sando, Lead Fraud Management Analyst at Javelin Strategy & Research, discussed how robust ACH fraud monitoring controls can do more than satisfy regulatory obligations—they can act as a proactive risk prevention mechanism. This is essential to combat the growing prevalence and complexity of fraud.
The Importance of Trust
The compliance aspect of ACH fraud monitoring is partly driven by the latest version of the WEB debit rule, instituted by Nacha—the organization that governs the ACH network. Nacha’s enhanced fraud monitoring requirements raise expectations for all participants in the ACH ecosystem.
“It increases the bar to say that we’re not just checking the validity of the account, but we’re also doing fraud checks,” Gordon said. “It creates an opportunity for financial service providers to identify fraud and to look at the potential risk associated with a consumer.”
“It moves beyond compliance for compliance’s sake, which creates a lot of opportunities for financial service providers to not only identify and reduce fraud, but to put consumers in the right products that create mutually beneficial paths for them,” he said.
Finding the right fit with customers has become more challenging in the digital era, where consumers have more options than ever and increasingly expect efficiency in every interaction. As a result, consumers often choose the path of least resistance when selecting a financial institution.
These factors place institutions in a precarious position: they must balance security with customer expectations, both of which significantly impact retention.
“The importance of consumer trust cannot be overstated,” Sando said. “We’re finding that when consumers have experiences with fraud or scams on a particular account—whether it’s a traditional financial account like your checking or savings or a merchant account—if they’ve experienced any sort of suspicious activity or fraud and scams, they’re much more likely these days to close an account where the fraud occurred and move somewhere else.”
Stepping Up Authentication
Given the risk of attrition, account onboarding and authentication have become critical stages in the customer experience. One key challenge arises from misapplied friction, where every user is forced to undergo the same verification process regardless of risk profile.
“Our belief is there’s enough value in customer data that it can be managed through step-up authentication, that you are injecting friction where friction is warranted based on the risk signals that consumers have in concert with their profiles—whether that be their bank account, their payment transactions, or their credit scores,” Gordon said.
“There are a number of different ways to end up at the right answer so that you’re facilitating a flow where the consumers stay in the process and you are fast tracking your low-risk consumers and putting obstacles in place where they should be,” he said.
This process can be optimized by leveraging the richer data available in a validated account. Institutions can go further by authenticating the account, confirming that the applicant’s name matches the account owner’s—allowing for a more targeted, efficient approach.
Implementing these measures early in the process is critical for fraud prevention and enables a customized experience, reducing the verification burden on the institution.
For example, if a consumer opts out during onboarding due to friction triggered by their financial profile, the institution avoids a potentially difficult credit decision. Conversely, highly qualified consumers can be fast-tracked, improving both the experience and conversion rates.
Scouring Alternative Data
Although authentication is vital, it is increasingly challenging under the current credit scoring system. Last year, traditional scoring methodologies eliminated medical debt—a significant portion of consumer credit—from scores. While this change reshapes scoring, it does not remove the underlying debt burden.
Additionally, consumers now maintain more financial relationships than ever, including accounts at traditional banks, digital-first banks, and fintechs. Many of these relationships are undisclosed, complicating accurate assessments of creditworthiness.
“It becomes incumbent upon financial service providers to look at alternative data in a way that they can derive value out of it,” Gordon said. “We believe the consumers’ bank behavior, their payment success rates, and the velocity with which their PII elements change are all clues that will lead you to have a more accurate picture of that consumer—what they can afford and their creditworthiness.”
“When we factor in the way that consumers acquire credit today versus the way they did in 1989 when the FICO score was created, they’re wildly different,” he said. “The traditional scoring methodologies haven’t kept pace with the way consumers are acquiring credit now. We see scenarios where consumers apply with a clean bank account only to subsequently change to a neobank account or some other bank account that they’re utilizing to enact what equates to first party fraud.”
Palatable to All Parties
These challenges have driven the emergence of data-driven treatment strategies, where financial service providers leverage shared industry data. This intelligence provides critical insights into connections between consumers, accounts, identities, and performance metrics.
Such knowledge enhances underwriting, creating a scenario where a consumer’s application experience is guided by both their inputs and industry knowledge of past activity. However, these strategies must always be aligned with the institution’s broader objectives.
“We have a client that we work with that does account-to-account payments tied to loyalty cards,” Gordon said. “Their exposure in that scenario is fairly limited, they want as much acceptance as they can possibly get. Conversely, we have some clients who are doing large dollar distributions, and it is not too much to ask for someone to credential into a bank account and we’re talking about the potential for five- and six-figure disbursements.”
“It’s difficult to ensure that you’re keeping down the cost of doing business, the fraud losses, and ultimately the cost of credit,” he said. “When you marry the authentication process to the use case, you end up with a lot better solution that’s more palatable to all parties.”
Confidently and Compliantly
Developing strategies and implementing fraud management measures is imperative, as new and potent fraud variant emerge daily. The most effective defense is sharing information and leveraging a risk intelligence provider to help chart the way forward.
“It’s finding a solutions provider that is flexible and can adjust and be agile in the same way that we find fraudsters are agile with technology and how they can use it against consumers,” Sando said. “It’s also about recognizing the fact that consumers are not all the same, it’s not one-size-fits-all. It’s about having that solution provider that can help you figure out how we navigate each individual case to make sure that it’s optimized for every single customer that comes through the system.”
These solutions help organizations stay ahead of escalating fraud threats and maintain compliance with regulations like Nacha’s rule enhancements. But that’s just the beginning.
“There is a lot of opportunity beyond compliance in account verification and authentication,” Gordon said. “What we see is that not only will more of your payments clear, but there are certain attributes and thresholds that , when crossed, significantly improve performance. Meaning, you’ve verified the account, the account has a certain history, and it doesn’t indicate any of the negative attribution that we often see compounded by a name match. You have the ability to operate confidently and compliantly in a way that you probably aren’t enjoying at present.”
The post From a Checkbox to a Differentiator: Redefining ACH Fraud Monitoring appeared first on PaymentsJournal.
30 March 2026, 1:00 pm - More Episodes? Get the App